|
|
 | Build your own private intelligence agency. Travel around the world, trade with state secrets, weapon systems, spy codes, WMD, hire secretaries, agents, lawyers, helicopters and soldiers, establish agency stations, cells and bases and search for criminals and politicians. Involve in spy game. Game c...
|
 | Codename Alvin PC Spy allows you to monitor keyboard, internet, screen and application activity with ease. Great to keep an eye on what your kids are up to when your not there, or your staff! Easy to use and cheap to register, free download is available so you can try the software fully before regis...
|
 | Codename Alvin PC Spy allows you to monitor keyboard, internet, screen and application activity with ease. Great to keep an eye on what your kids are up to when your not there, or your staff! Easy to use and cheap to register, free download is available so you can try the software fully before regis...
|
 | Build your own private intelligence agency. Travel around the world, trade with state secrets, weapon systems, spy codes, WMD, hire secretaries, agents, lawyers, helicopters and soldiers, establish agency stations, cells and bases and search for criminals and politicians. Involve in spy game. Bikini...
|
 | Wireless WEP Key Password Spy will instantly recover all WEP keys and wireless network passwords that have been stored on your computer. To get started, click "Find Wireless WEP Keys". It will then display the adapter GUID and all recovered information associated with it including the wireless netwo...
|
 | Automatically record incoming & outgoing telephone calls using sound card; Caller ID detection via the same sound card; DTMF keys detection; Auto Gain control; Multiple sound cards/32 telephone lines supported; Perfect hidding mode....
|
 | Spy Sniper is an award-winning spyware, malware, and adware detector, remover, and shield, now with a new and more advanced spyware detection algorithm and one of the largest spyware /adware databases in the world. Spy Sniper also includes a stealth feature which allows you to use its features while...
Tags: anti spyware, detection, prevention, spyware, adware, malware, anti-spy, clean tracks, detect spyware, scan, shield, |
 | Spy Sniper is an award-winning spyware, malware, and adware detector, remover, and shield, now with a new and more advanced spyware detection algorithm and one of the largest spyware /adware databases in the world. Spy Sniper also includes a stealth feature which allows you to use its features while...
|
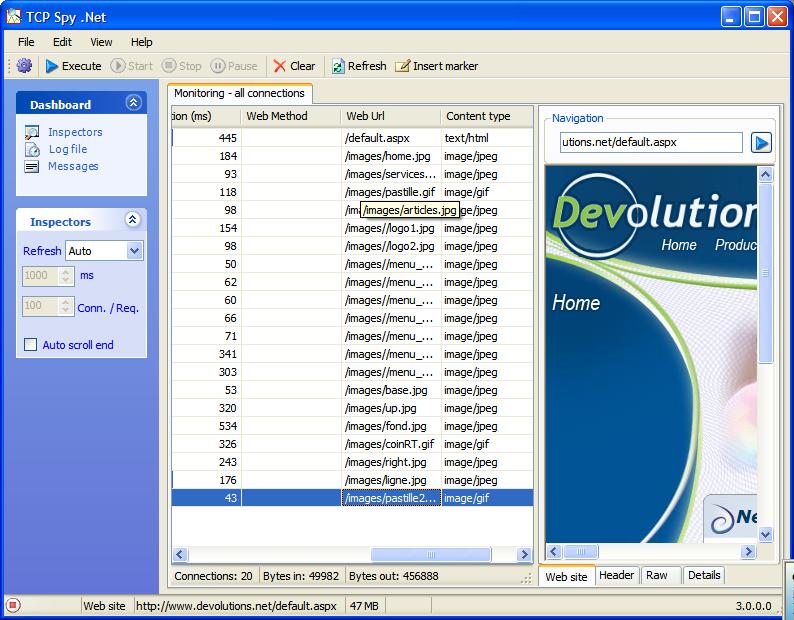
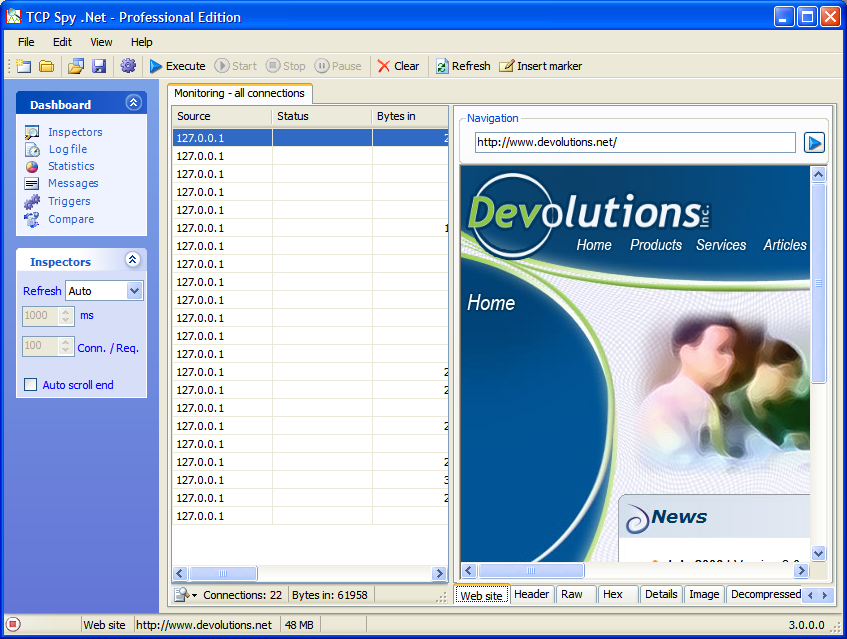
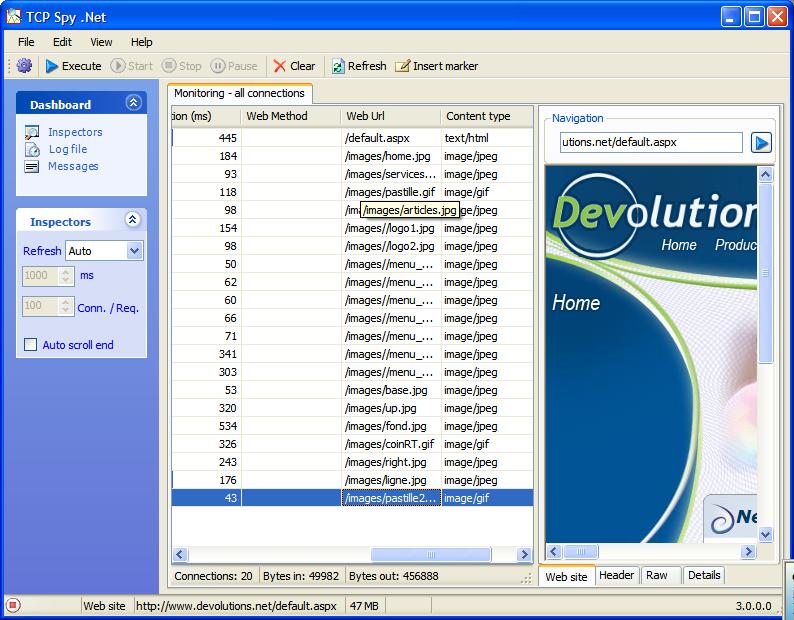 | TCP Spy .NET is a small application used to trace TCP packets between a client and a server. Optimized for .NET Web Services or Web Site TCP Spy .NET will help you find any bottleneck and it will help you in analyzing your bandwidth usage. With TCP Spy .NET, you can inspect data in different views, ...
|
 | Yahoo! Messenger Spy Monitor spy software can secretly record all Yahoo! Messenger incoming and outgoing chat text messages. It runs in a complete invisible mode. You can check all recorded messages by simply receiving emails or opening a web page. The re-check merchanism can ensure you get the whol...
|
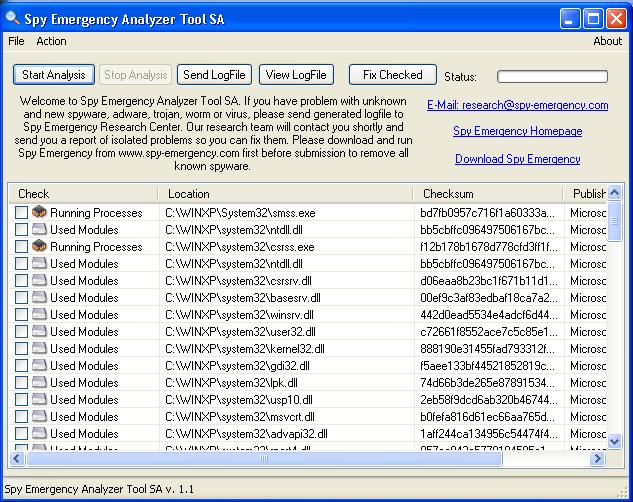
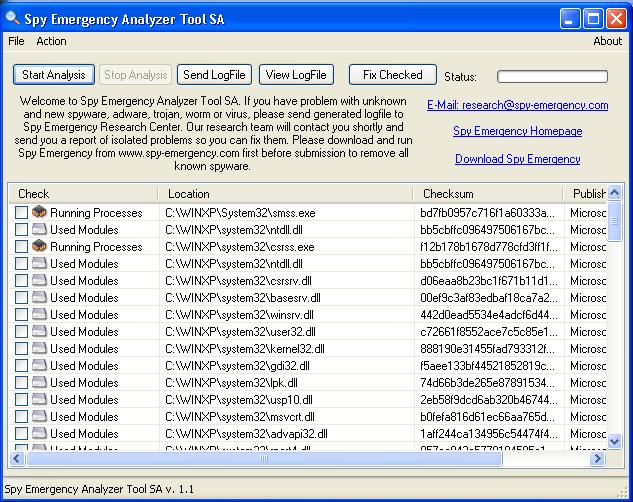 | Spy Emergency Analyzer Tool lists all critical areas of your PC like startup programs, BHOs, running programs and loaded libraries. It helps in situations when you have been infected by new and unidentified spyware, adware, keylogger, trojan or worm. A generated log file can be send to Spy Emergency...
|
 | TCP Spy .NET is a small application used to trace TCP packets between a client and a server. Optimized for .NET Web Services or Web Site TCP Spy .NET will help you find any bottleneck and it will help you in analyzing your bandwidth usage. With TCP Spy .NET, you can inspect data in different views, ...
Tags: tcp, http, smart client, profiler, |
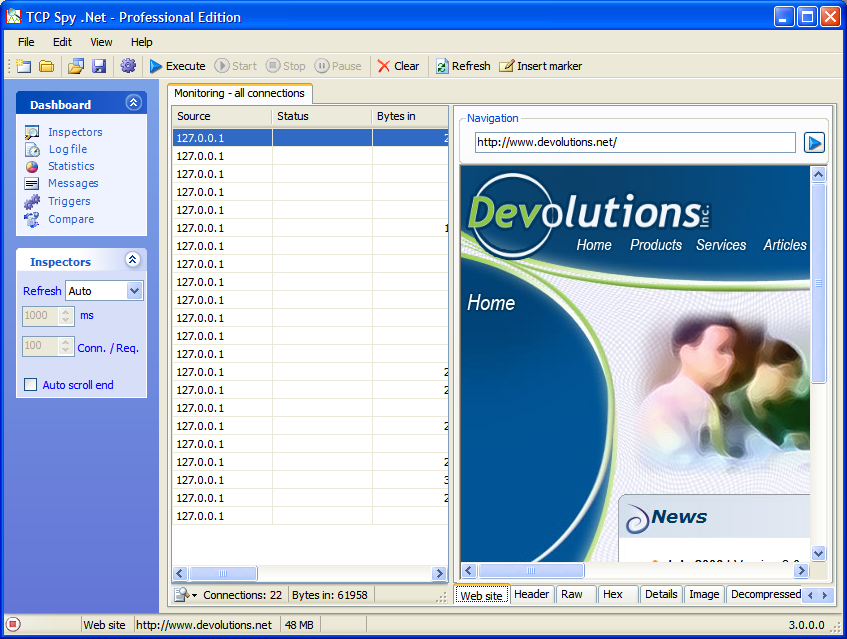 | TCP Spy .NET is a small application used to trace TCP packets between a client and a server. Optimized for .NET Web Services or Web Site TCP Spy .NET will help you find any bottleneck and it will help you in analyzing your bandwidth usage. With TCP Spy .NET, you can inspect data in different views, ...
|
 | IMMonitor Yahoo Messenger Spy allow you to monitor, block or record Yahoo Messenger conversations remotely, If your kids (or spouse!) are spending too much time chatting via Yahoo Messenger, or you suspect they're engaged in dangerous conversations, IMMonitor Yahoo Messenger Spy is a very simple way...
|
Knanaya - Fetch Rewards - Coin Slots - AKB48 Yuko Photo Puzzle Game - Bonusbogen -
 | A bot is a program used to automatically play poker in an Internet poker game. It is programmed to play in a certain way based on mathematical formulas. Hour after hour, as long as the game continues, the bot plays tirelessly on. You do not need to know anything about poker to win. Simply let Holdem...
|
 | EMF2PDF(Metafile,EMF,WMF,RTF To PDF) converts enhanced metafiles and Rich Text Format (RTF) to PDF while preserving the vector and text information.This results in small PDF files which can be printed at high resolution. Metafile/EMF/WMF/RTF To PDF converts Rich Text Format (RTF)file to PDF file doe...
|
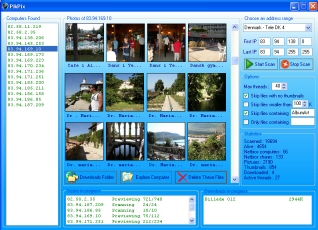
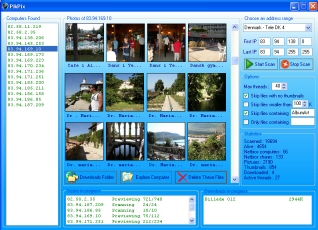 | PikPix gives you access to the pictures shared by any user on the internet. In a quick and easy way, millions of high-res, amateur and never seen before pictures on your pc. PikPix can access a limitless number of pictures by performing a netbios scan on any IP address range. It will automatically d...
|
 | PikPix gives you access to the pictures shared by any user on the internet. In a quick and easy way, millions of high-res, amateur and never seen before pictures on your pc. PikPix can access a limitless number of pictures by performing a netbios scan on any IP address range. It will automatically d...
|
 | AIM Monitor Sniffer is network utility software designed to monitor, record and capture AIM (AOL Instant Messenger) chat conversations on all computers in a network. It is able to record all conversations automatically and export all intercepted messages to HTML files for later processing and analyz...
|
 | ICQ Monitor Sniffer is network utility software designed to monitor, record and capture ICQ chat conversations on all computers in a network. It is able to record all conversations automatically and export all intercepted messages to HTML files for later processing and analyzing. It is very easy to ...
|
 | Permanently deleted important messages? Lost access to email after a system failure? Corrupted DBX database? Get back your email and restore Outlook Express operation in a matter of minutes! If Outlook Express crashes while accessing a DBX file, you’ll lose access to your email archive – but not...
|
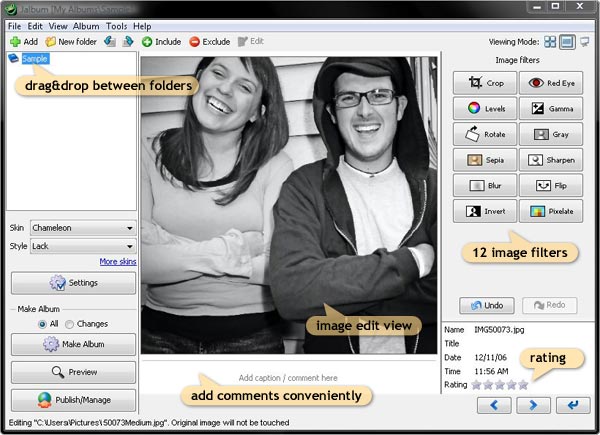
Jalbum (in Cataloging)
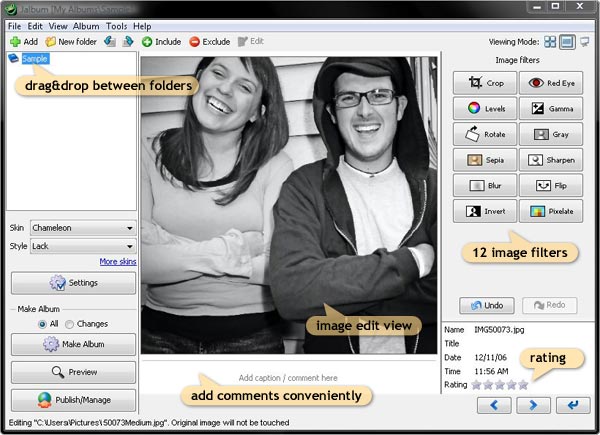 | Create web albums from your digital photos, or any file, just the way you want it with this award winning software. It's free - and there is no catch! - Manage your photos Jalbum has a built in image editing features for basic image re touching and a file handling system. Polish the photos you like ...
|
 | I want to share with you my experience of using Keylogger King Pro. In our department, we use several methods of work-time effectiveness control. One of them, a daily report, was our best achievement so far. Yet, I was unable to precisely determine the time needed by our employees to finish certain ...
Tags: spy software, keylogger, key logger, hardware keylogger, keystroke recorder, keystroke logger, keytrap, invisible keylogger, keyboard logger, keyboard monitor, keyboard monitoring, keycopy, keystroke recorder, keystroke recorder, |
 | Information...priceless! Modern programs do their best to protect you from data loss. Text editors create backup copies of documents, web browsers remember login info that you enter on Web pages. Password managers help you manage your passwords, backup managers help you backup virtually everything. ...
|
 | You are buying a computer for your kids. You purchase tons of educational software for them so they can increase their IQs. You pay for a broadband Internet connection to allow your kids to absorb useful information. And what happens? Instead of using the computer for good, they end up playing stupi...
|
DBF Manager (in Database Management)
 | As technology advances we tend to switch to new ways of accomplishing the same tasks. Faster machines and better software increase our overall computing and information processing speed as well as overall comfort and reliability. New solutions sometimes offer expanded functionality and increased per...
Tags: dbf, clipper, foxpro, dbase, dbf viewer, dbf editor, view dbf files, edit dbf, dbf structure, dbf file index, reindex, dbf order, ntx, cdx, ndx, dbf, dbf format, dbf structure, dbf file viewer, dbf file editor, cdx viewer, cdx editor, open dbf file, dbf file structure, |
 | The purpose of this program is to find all mp3(ogg,wma) duplicates on your computer and remove useless files from your hard drive. As this program performs just this single task it copes with it much better than other more universal programs. Unlike the other programs for duplicate files search, our...
|
 | The purpose of this program is to find all mp3(ogg,wma) duplicates on your computer and remove useless files from your hard drive. As this program performs just this single task it copes with it much better than other more universal programs. Unlike the other programs for duplicate files search, our...
|
|
|